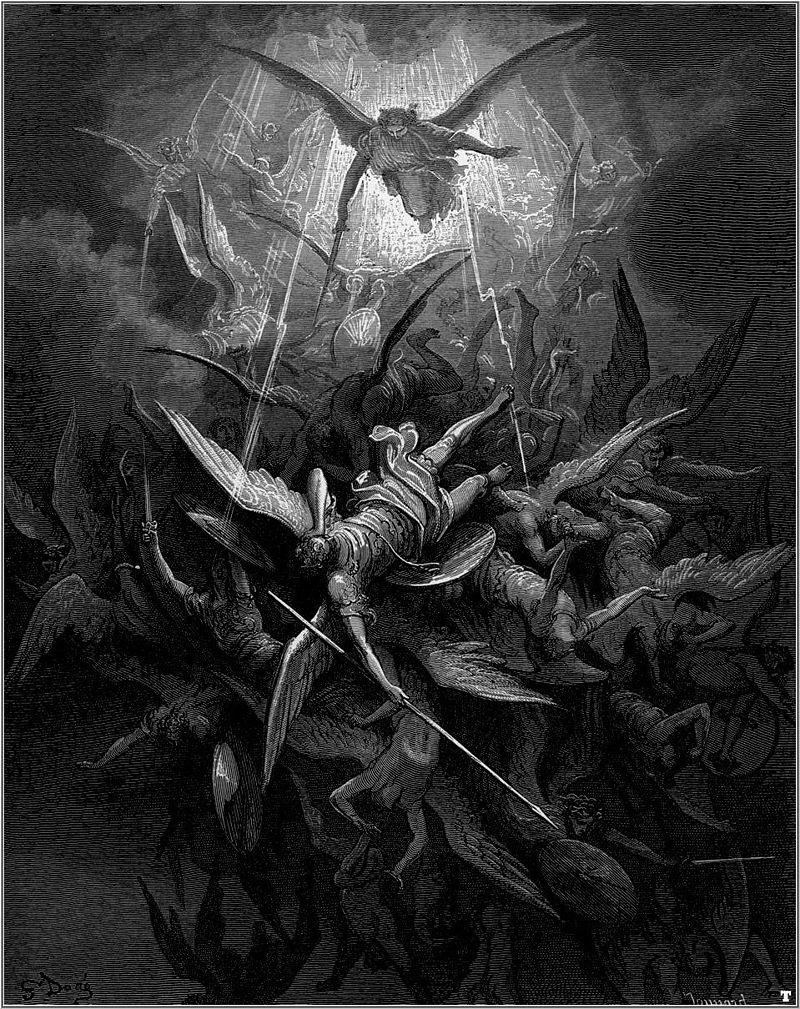
Michael casts out rebel angels. Illustration by Gustave Doré for John Milton's Paradise Lost
Belief /biˈlēf/noun
1. an acceptance that a statement is true or that something exists.
2. trust, faith, or confidence in someone or something.
Where Do You Stand?
Do you believe your data is secure because of the word “secure” placed where you can see it?
Do you believe that your data is safe because it is password protected?
Do you believe no one has your data because it is protected by an SSL certificate?
It’s the 21st century, appropriately coined “The Information Age”. It’s easy to be overloaded with information and misinformation. Every day you are targeted by marketing campaigns designed to persuade you to buy something, be it peace of mind or something claiming to be useful. Some are legitimate and some not so much. Believing that a site is secure by “blind faith” is not enough in regards to your personal or financial information. How do you know that the merchant or charity that is taking your credit or debit card information is handling it seriously and securely? What are you doing to personally safeguard your personal, health, and financial information?
The Angels
Protection of your private information takes place at various levels all across the globe. Financial institutions and various governing bodies have an inherent need to ensure that the public’s private information is safeguarded. Laws are created to protect consumers and businesses alike in regards to safeguarding personal and financial information. There are various laws in every country and state or province. It may not be easy to become familiar with the ones that apply to your jurisdiction, however a good source for this information is DLA Piper’s Data Protection Laws of the World.
Outside of the law books and governing bodies, some service providers also do their fair share to protect your data by employing the use of firewalls, web application firewalls, data encryption, two-factor authentication, biometrics, as well as proper access control, separate of duties, and segregation of networks. There are also people all over the world devoted to discovering and patching vulnerabilities as they arise and ensuring software and hardware providers are patching their products. Yet, it’s simply not enough to keep sensitive data protected.
The Demons
With the increasing rate of discovered vulnerabilities, advances in technology, insecure networks, and weak passwords, the numerous safeguards that the government or any institution that handles your data implement could be for naught. It may come as a surprise to you that there are two vulnerabilities discovered every second. That increases the potential of your data being exposed to enormous proportions. With increasing advances in technology and the ability to garner substantial computing power with very little investment, it’s a race to prevent breaches before they occur.
The security of your information starts with you. There are products like oclHashcat that uses technology ,very similar to the programs used for mining electronic currency, that boast the ability to attempt eight million password guesses per second provided the attacker has a high end graphics card in their personal computer. Couple that with a weak password and you’ve essentially “thrown your pearls before the swine”.
See http://www.bmyers.com/public/1958.cfm for top 500 commonly used passwords, if you are using any passwords listed there, or even just a simple dictionary word, change it to something less easily guessed immediately! Attackers have a wealth of dictionary based password lists they try against. It is recommended that passphrases are used, rather than a simple password. So instead of simply using “rooster” as a password, you could use “TheRoosterCrows@6”. Also remember not to use a password you have used prior to the Heartbleed vulnerability being fixed (April 7, 2014), there is a very good chance that your password has been leaked and is on a stolen password list.
The Reality
While laws and regulations may stipulate requirements for third parties to uphold when taking your personal or financial information, it’s a false sense of security in reality. Just as gun laws do not prevent criminals from obtaining guns, these laws that require safeguarding of information do not prevent criminals from obtaining your personal or financial information. Over the last twelve months some major vulnerabilities and breaches have taken place. The responsibility for protecting personal data lies not only with the provider of data services, but also with the owner and/or provider of that data.
It’s an invisible war going on for your information. Governments, corporations, media, and advertising agencies are collecting more and more about you, because to them it’s business as usual. However, malicious attackers are just waiting for you to hand over your information so they can steal it and do a number of malicious things with it, from assuming your identity, laundering your bank account, or simply selling your information to the highest bidder. A breach happens when there is a failure of controls that are in place to protect things like data, equipment, persons, or places. You may not have control over how others handle your data, but you do have the ability to protect yourself and control over where you enter that data. It may take some effort but it will be well worth it if you are able to prevent malicious actors from being able to steal your information.
Take the time to review some of the most famous breaches of the last twelve months and really think about how safe your data is.
Sample of breaches within the last 12 months
- Heartbleed: An OpenSSL encryption bug was disclosed on April 3, 2014 that allowed third parties to capture sensitive information. Many big names (Amazon, Reddit, Tumblr, and WordPress) were susceptible to Heartbleed (http://heartbleed.com/).
- iCloud: A breach in Apple’s iCloud that exposed many celebrities intimate photos, even those believed to be deleted years ago due to cracking simple passwords. (http://www.huffingtonpost.com/2014/09/01/icloud-bug-fixed_n_5748642.html)
- Target: A massive breach of its point-of-sale terminals in December of last year affected an estimated 70 million shoppers. (https://corporate.target.com/discover/article/Important-Notice-Unauthorized-access-to-payment-ca)
- Adobe: A reported 38 million customers were affected by the breach that took place in October of last year. (http://krebsonsecurity.com/2013/10/adobe-breach-impacted-at-least-38-million-users/)
- Facebook, Google, and Twitter: Two million user accounts were affected by a social media attack last year. (http://money.cnn.com/2013/12/04/technology/security/passwords-stolen/)
- LivingSocial: An estimated 50 million user accounts were accessed by attackers. (http://www.bna.com/livingsocial-reveals-cyberattack-n17179873787/)
- JP Morgan Chase: In July of last year the bank discovered a breach to its website and that their personal information may be compromised. (http://www.reuters.com/article/2013/12/05/us-jpmorgan-dataexposed-idUSBRE9B405R20131205)
- University of Pittsburgh Medical Center: Employee information was scammed and enabled the attackers to file fraudulent 2013 tax returns. (http://www.post-gazette.com/local/city/2014/05/30/All-62-000-workers-at-UPMC-may-now-be-victims-Data-breach-at-UPMC-may/stories/201405300188)
- Comcast: Thousands of unlisted phone numbers were leaked threatening customer privacy. (https://www.eff.org/deeplinks/2014/08/comcast-data-breach-leaks-thousands-unlisted-phone-numbers-threatening-customers)
- UPS: A breach that compromised over a hundred thousand transactions made by customers from January to August of this year, leading to possibly stolen credit/debit card data. (http://www.techtimes.com/articles/13624/20140821/ups-reports-security-breach-customer-data-compromised-at-51-franchises.htm)
- IRS: Contractors were allowed access to taxpayer data without appropriate background checks, which is a severe policy violation. (http://www.treasury.gov/tigta/auditreports/2014reports/201410037fr.html)
Avoid a Personal Apocalypse
No matter where you store sensitive data, whether on your computer, your phone, the cloud, external storage, or on a USB stick, you are still at risk. Sensitive data is everywhere. The POS systems at any store where you swipe your credit or debit cards, your financial institution, your health providers, the local, state, and federal government entities, your utility companies, your phone, internet and cable service providers, your schools and colleges, even your place of employment are potential targets. The first step in protecting your data is by ensuring you aren’t protecting it with a weak password. Remember, it’s not how a breach may occur, but a matter of when. At some point, some sites or applications you use may end up exposed to attackers that will be more than happy to take that information and use it for nefarious purposes.
Do not use the same passphrase across multiple sites. Use unique passphrases for financial sites and keep them separate from the ones you use for random forums and a different one for any utilities or other merchant sites you use to shop online. Use a payment service to limit access to your financial data where you can. If you have the option to use two-factor authentication for any of the places you do business with, choose it over using a single password or passphrase. If you must store your passwords/passphrases and sensitive data locally or in the cloud, store them encrypted by using services like Folder Lock, Advanced Encryption Package Pro, or Dekart Keeper. If you don’t have anything other than passphrases you need to keep private then use products like: LastPass, PasswordBox, or Dashlane.
Ensure you clear your cookies after every online banking/shopping/bill paying session (http://www.wikihow.com/Clear-Your-Browser%27s-Cookies). Ensure that any site you log into is protected via SSL. If it is, you should see https:// at the start of the URL in your browser’s address bar.
Consider using a payment service, like Google Wallet, ProPay, Dwolla, WePay, Skrill, and PayPal, rather than entering your credit card data into various merchant sites that you aren’t sure you can trust.
Easy Security Checklist
| 1 | Is your login SSL protected? | Check for the requisite https:// at the beginning of the URL in your browser’s address bar! https://www.ultratools.com/tools/sslExam Paste the link of any site into this one and check for a valid certificate. |
| 2 | Check for Heartbleed | https://filippo.io/Heartbleed/ If vulnerable – inform the site owner and stop using the site until it’s fixed – when it’s fixed change your passphrase. |
| 3 | Clear Cookies | http://www.wikihow.com/Clear-Your-Browser%27s-Cookies After any online session in which you used a passphrase to sign in where sensitive information is stored. |
| 4 | Opt for 2-factor Auth | Opt for this where you can for most financial or healthcare sites. This may require an app to be installed on your phone or for you to carry a key fob. |
| 5 | Use Different Passphrases | Use unique passphrases across all sites where you store sensitive data. Don’t use the same password for twitter that you use for your banking! |
| 6 | Don’t use Weak Passwords | http://www.bmyers.com/public/1958.cfm If your password is in this list or matches a dictionary word – change it immediately |
| 7 | Encrypt your Sensitive Data |
Data Encryption
Site Logins and Passwords Only
|
| 8 | Weigh the Risk | Before you upload that image or enter sensitive information into a site, weigh the risk. If you are uncomfortable with the information being made public, it’s probably best not to put it on the internet at all. This includes e-mail, the cloud, online storage, text messages, etc. |
| Evangelize These Tips | Protect your friends and loved ones by informing them. |




