- RECENT
- POPULAR
- SHARED
If the rats are after your cheese, keep the cheese safe
Jason Ha explores how can we prevent hackers from taking a bite out of our assets.
Is Your Security Framework Like a Smooth Saloon Car or a 4X4?
If we took the same approach to building a car as we did to our organisational controls and capabilities what would be the result? Jason Ha takes a look under the bonnet.
Waiting for Godot and a Data Breach
Indy Dhami joins Estragon and Vladimir and looks at what Waiting for Godot can teach us about the attitudes companies should adopt towards security threats
Lessons From the Pit Lane
Anne Wood takes inspiration from Formula 1, and discusses how understanding our environments is crucial to having the winning infosec strategy.
Digital Vampires
Dixie Newman lifts the coffin lid on the vampire, and how they can hunt and feed upon us in the digital world too.
The importance of the captain’s log…
How can we ensure our IT management is smooth sailing? Emmanuel Nicaise sails the infosec sea and considers how to steer clear of stormy weather.

Jurassic Park – Based on a True Story…
Yes, really!I was recently looking for a change of direction in my information security career and was invited to an interview at a local company. I was instructed to prepare a 10 minute presentation on ...

Lessons from the Big Four – Shakespeare’s Tragic Heroes
I don’t know if the phrase “the bigger they come, the harder they fall” was around when Shakespeare was alive but it applies to his tragic heroes across the board. If we look at his ...

God Save Me From My Friends. I Can Protect Myself From My Enemies
This quote is attributed to many. In fact, most people believe it was first said by King David himself. Some attribute to the French philosopher Voltaire, and others to the French marshal Claude Louis Hector ...
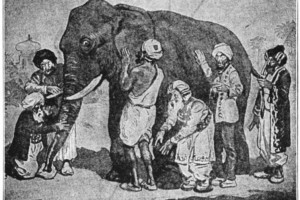
The Elephant and the Six Blind Men: What Does Information Security Mean to You?
The poem “The Blind Men and the Elephant” was written by John Godfrey Saxe (1816-1887). The essence of the poem is that their reactions were: The first felt the side of the elephant and said: It’s ...

Don’t Walk on the Grass!
In a vain bid to keep fit, I go running. Sometimes. When the mood takes me. It’s one of those things that I know I should do - I understand the importance of exercise, but ...

The Story of the Suicidal Kangaroo
Another identikit hotel room – I know the layout with my eyes shut. The desk will be five steps to the right. The TV remote control will be on the pillow and there will be ...
Like Juliet On The Balcony…
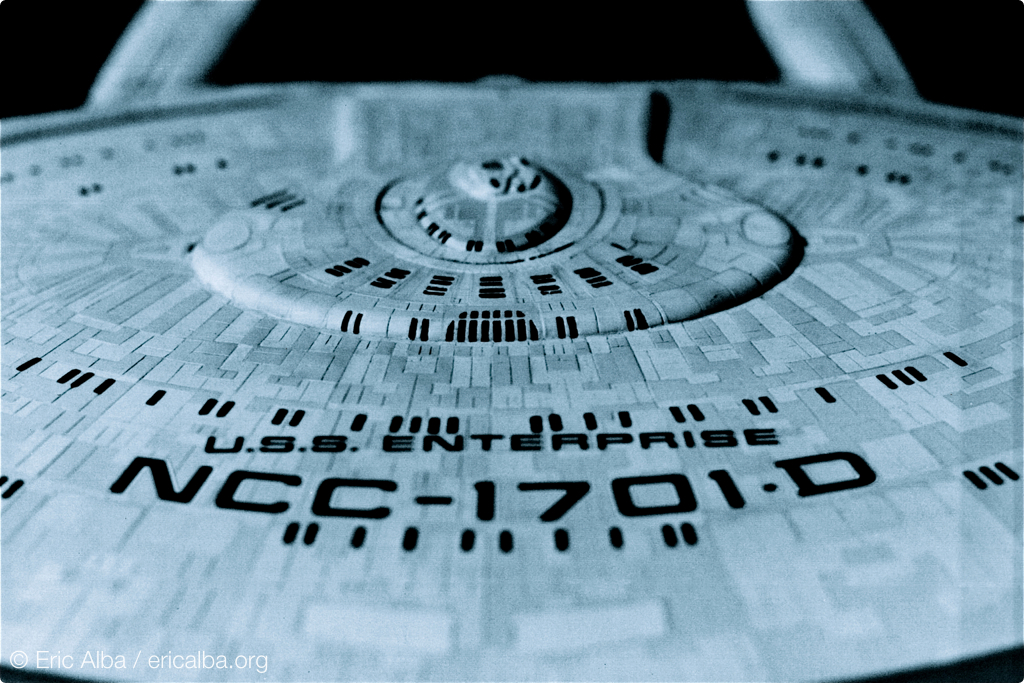
Andy Jones transports us into the world of Sci-Fi and looks at what interspecies communication in Star Trek teach us about spreading the InfoSec message.
The Flute and the Fortress
From 15th Century Constantinople & Bible stories to French Philosophers. Frank Wintle explores the idea that human beings might simply be incapable of keeping a secret.
The Tower of Babel and the Vocabulary of Risk Management
Eduardo Gelbstein delves into the language surrounding Information Risk Management and looks at how assigning different meanings to words we think we understand remains a challenge.
What’s that Plumber Doing in the Bedroom?
How much access would you give to a tradesman in your own home? Stuart Facey explores the levels of freedom we give to third parties within our organisations and how we can make them, and our homes, more secure.
Ønske: Udvikling videre fra skyttegravskrig
This is the Danish version of ‘Evolving Trench Warfare’ first published on the 10th November 2014. As a result of trench warfare, countless soldiers died during World War I. Claus Houmann takes at who was responsible and how this can relate to modern day security breaches.
Piracy and Letters of Marque
From piracy on the high seas to today’s battles online. Claus Houmann looks at how the battlefield may have changed, but what about the rules of engagement?