
Photo Credit: Lee Bennett via Compfight cc
Embarrassing Exposure, Unforeseen Security Incidents & Proper Planning
I was in London. It was the night before a presentation to about 50 senior staff from various companies on supplier security governance. It was kind of last minute and on the train down I realised the slide deck I’d intended to reuse was ‘off’ in terms of the audience (security management focussed deck for an IT management focused room). I resigned myself to rewriting it overnight.
I was pretty blurry by 2am. I went to put my room service tray outside the door while holding it open with my foot…
…then my foot slipped.
Not so bad? Well it wouldn’t have been it I’d had my trousers on! After doing that thing where you stare at the door not accepting that it’s happened, my trusty incident management skills kicked in…kind of:
Plan A: Use covert ops style tactics to reach reception unseen and subtly flag the attention of a staff member…
…BAD idea. Facing reception meant standing in a brilliantly lit foyer with my back to a wall of glass looking out onto a main London thoroughfare. I felt unable to take responsibility for the vehicular mayhem that may have ensued.
Plan B: Wait for someone to come along…
…but no-one did. It was very chilly, I felt very silly and I was suddenly feeling effects of pints of coffee.
Plan C: Knock on a door…
…which I did. Cue one very surprised, confused then slightly hopeful looking fellow in his 50’s. He let me use his phone then gathered himself to make very British small talk until a suitably underwhelmed looking staff member showed up.
Despite those adventures all went incredibly well the next day. Perhaps because I’d thoroughly put any stage fright into perspective!
“Ho, ho, very funny, I’d never do that” I hear you cry.
Really?
In a team-building session there was one of the usual ice-breaker type activities. Anonymous ‘secrets’ were put on slips of paper and folk who picked them out had to guess who they belonged to. One was:
“I was in London and got locked out of my hotel room naked”
A good chuckle was had by all. Then other such incidents (including mine) started to come out. In a room of about 30 people it turned out that roughly 20% had done the same (or a similar) thing.
Why am I telling you this? Because people don’t plan for this stuff. It’s not in our nature to do so until it happens to us, someone we know, or someone unlucky enough to have it shouted about on the internet. Even then we can forget the potential or actual pain and lose motivation to plan, if fallout THAT TIME didn’t seem bad or relevant enough.
To break down the lessons I see in my London adventure:
Excuse language, but shit happens
Estimating the probability of an impactful security incident is not easy, but there are sensible scenarios you should examine and plan for. For outlier events you can map them to suitable planned responses. Simply mobilising key staff fast can make a world of difference.
Here is my take on events that account for the overwhelming majority of expensive and/or newsworthy breaches:
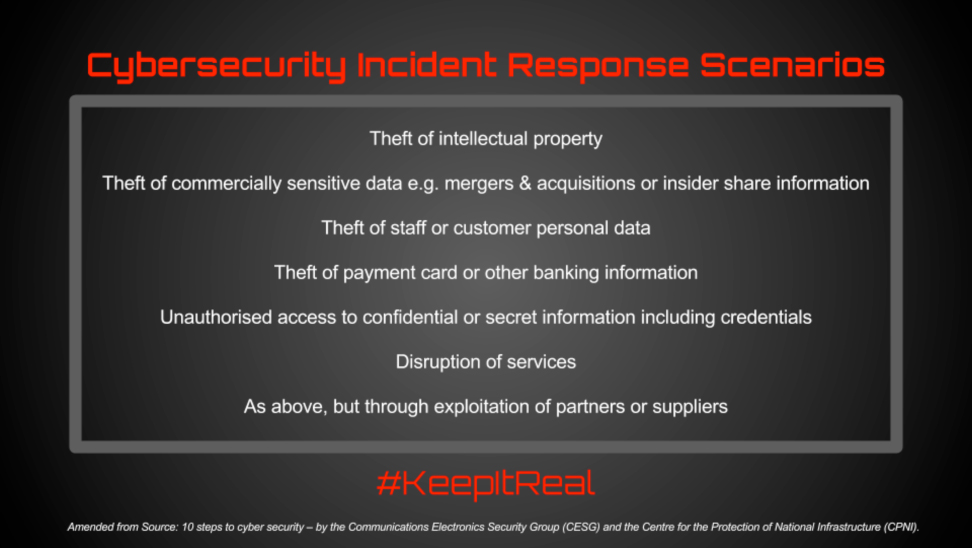
The plea to keep it real is aimed most at businesses who confuse availability and security incident scenarios. There is crossover, but too little real testing of data loss events goes on.
As a related aside, the keep it real plea could also be aimed at IT Disaster Recovery planning. I’ve seen a DR exercise suggested for loss of both primary and backup data centres and memorably (this was a genuine suggestion from a senior manager), for an asteroid strike. The offline response to the latter was:
“If that hits the news, the last thing I’m going to be doing is finding my copy of the response plan”
Having said all that, hard to predict ‘outlier’ incidents do still have a place in plans
Black swans
The unpredictable (but curiously not perceived as rare) stuff, gets redefined all the time. What was once not foreseeable, becomes predictable when sufficient data to note longer term trends becomes available (like the team day revelations). Keep an eye on developments in incident trend analysis and integrate learnings into your risk and incident management effort.
In a specific security example, no-one outside the hard core of security experts, really believed a Stuxnet type attack was doable…until it was done. Now you can’t venture into any security related internet space without tripping over talk of APTs.
Not all practiced plans fit incident reality
Be flexible with planning. Your internal and external environment might not match what you foresaw when diligently running the team through response to a breach (think plate glass showcase for my trouserless rear view). Build consideration of that into the process.
It won’t happen again
On that question of ignoring minor incidents, not planning, then getting caught by a biggie, that wasn’t the first time something like that had happened to one of those people. There was an utterly understandable and innocent explanation, but it’s still TMI for this analogy.
Proof that lightning, however rare, can and does strike twice. So please don’t get lulled into a relatively incident-free false sense of security. You don’t want to be the one firm in this cyber-storm wandering round in an open field with your umbrella held high.
******************************
As a parting shot, there is (believe it or not), an incident response plan for those hotel scenarios
So what, in your far more serious security world, is your excuse?






