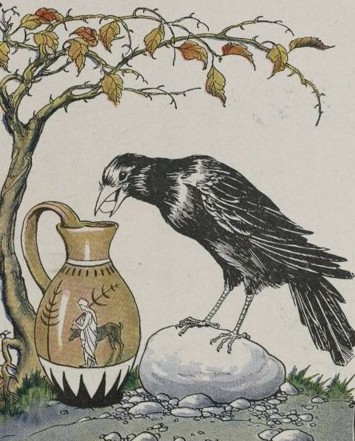
The Crow and the Pitcher From ''The Æsop for Children'', by Æsop Project Gutenberg etext 19994 http://www.gutenberg.org/etext/19994
Once there was a crow who was half dead from thirst when he came upon a pitcher of water. Although the pitcher had once been full, now when the crow tried to drink he could not get his beak far enough down into the pitcher through the restricted access of the neck to get to the liquid.
The crow looked around and saw a pile of pebbles on the ground. He reached over and dropped a pebble in the water. He could still not reach the liquid. So he dropped another pebble in the water. He still could not reach the liquid. He was by now very tired and thirsty but he continued to drop stones one by one into the water.
Eventually, he dropped a final pebble and pushed his beak in as far as it would go and managed to get to the liquid below. Once he has a small drink and was refreshed, he dropped the rest of the stones in the water and drank freely from the pitcher.
Once there was a hacker, who was tired and thirsty for knowledge. He really wanted a big score so that he could feed himself from the information he stole. He came across a big bank (Pitcher.com) and thought it looked ripe for the taking. He tried to attack it using the normal default passwords for routers, firewalls and building management systems. He did not get in. He decided that it would be a good idea to log on to Companies House and find out more about Picher.com. Armed with information about the chief exec and the company secretary, he phoned up and spoke to an administrator. She would not give him any access to her boss’s details, but she did confirm through her language that they still worked there. He did not get in.
Next the hacker thought he would check the print and online media for stories about the company including litigation and high profile deals. He took this information and tried a brute force attack with user IDs and passwords generated from his search. He did not get in.
He was a social person so next he tried social media and trawled Facebook and Twitter for people who said they worked for Pitcher.com. He found many promising leads and rated their vulnerability based on their social media security awareness. He still did not get in.
Finally, he went on to LinkedIn and selected the Pitcher.com alumni group. He found some recent leavers and analysed their backgrounds. From this he made more phone calls and eventually got an admin to reset a password on an old account. He got in.
Of course the hacker would not stop with one drink, once he was in, he continued to increase his spread and impact with more research and more data acquisition. It was not until later, when its commercial secrets were gone and the newspapers were full of its memos, that Pitcher.com wondered if it had a problem.




