
Photo Credit: 182nd Airlift Wing Flickr via Compfight cc
For any merchant or service provider storing, processing or storing customers’ cardholder data, which involves any supporting network systems, there is a requirement to carry out some form of security testing. Two of these security testing requirements are the need for quarterly internal and external (ASV) vulnerability scanning (11.2) and for a penetration test to be carried out annually, or after any significant change to the network.
Why is this?
Hackers are very intuitive and love a challenge, so are constantly looking for workarounds and innovative ways to undermine the integrity of these systems.
Consequently, IT managers consistently feel like they are ‘behind the drag curve’ and maintaining an secure network becomes a ‘war of attrition’. The requirement for quarterly vulnerability scanning and penetration testing is one of the ways for reducing these risks.
Okay, so we now know the terms but how can we relate to what these terms mean?
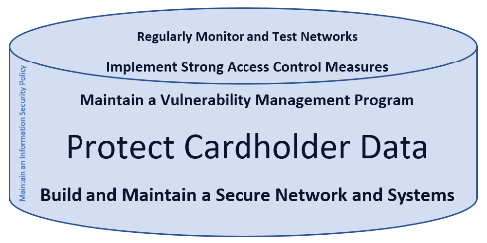
If you think of the 6 Goals of the PCI DSS as the layers of a wedding cake, protected in a cake box, the purpose of the top layer (monitoring and testing) is to confirm that the supporting layers are being maintained.
As an ex-RAF policeman, the best way to visualise this is to imagine your vulnerability scanner as being like your internal and external security, carrying out periodic internal and external patrols. During these patrols, they are looking for things like doors and windows being left ajar or holes in your fences. On discovery of such observations, the patrols send back a report to allow timely remediation before it can be exploited by any opportunist intruder.
The penetration test is an added mitigation control where a ‘known hostile’ is tasked to try to manipulate the in-place defences. For example, the patrols did not detect any doors or windows being left ajar, however, the penetration tester will manually rattle the handles to ensure everything is locked, or try to pick the locks of low grade door/window locks, or try to manipulate poorly maintained or implemented doors (e.g. popping the hinge pins, tailgating, etc.) – thus allowing unauthorised access to the areas within.
Consequently, in order to make the most effective use of the aforementioned countermeasures is to ensure that the security is effectively patrolling your networks and that you have a suitable vulnerability management and remediation programme in place. Once this is in place, look to task a highly skilled ‘known hostile’ to come and try to identify further hidden vulnerabilities.
Remember, if you’re not the one identifying and fixing these weaknesses it is only a matter of time before an ‘unknown hostile’ comes along and finds them. A ‘known hostile’ is limited by any pre-defined scoping and ‘Rules of Engagement’; an ‘unknown hostile’ is not!




