Photo Credit: ninjawil via Compfight cc
Bruce Schneier’s quote that “People are the weakest link in information security”, is probably the most famous in the profession. However, I have to say I am infuriated by the way it generally interpreted as almost an excuse for weakness in the information security process. In effect, it’s saying it is not the fault of the security people who valiantly strive to make systems secure; it is down to the weak user that we can do nothing about.
Now I have read Bruce’s books and I have seen him talk several times and I am confident that he did not mean this statement to be taken as an excuse. It was a challenge. Let me give you an analogy.
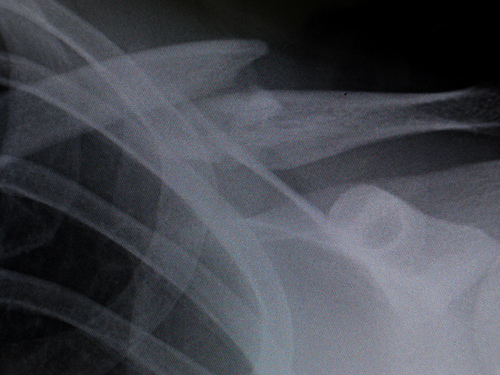
Last February, we had a weekend of very icy weather, during what was otherwise generally a wet winter. That weekend my husband fell and dislocated his shoulder. Now this is a very nasty injury; I’m told a broken limb is easier to recover from. However, at no time during the 6 hours in the Accident and Emergency department did a doctor or nurse say, “your shoulder will be weak – live with it”. Afterwards neither the surgeon, the GP nor the physiotherapist said “your shoulder will always be weak; Ho hum” On the same weekend a friend of mine, Mildred, who is 94 years old also fell in her garden and dislocated her shoulder. At no point in her treatment or recovery did anyone say to her “Mildred, you are 94 years old, your shoulder is going to be weak. Live with it”.
In both cases they had treatment and exercises, set and monitored by professionals, and they have both now recovered. Indeed, my husband’s shoulder is stronger than it has been in a long time.
Appropriately tackling the user interface in information security is a challenge. But doing it right can pay off with stronger, more resilient working practices. When there’s a significant injury it is not dealt with by someone who was once treated by someone who once saw a talk by a physiotherapist.
Security issues that have a significant impact on the security of operations demand the use of appropriate skilled help.
So let’s not see the ‘Weakest link’ as an excuse; let’s accept it as a challenge. Meet that challenge and build up the security practice in your organisation.




