- RECENT
- POPULAR
- SHARED
If the rats are after your cheese, keep the cheese safe
Jason Ha explores how can we prevent hackers from taking a bite out of our assets.
Is Your Security Framework Like a Smooth Saloon Car or a 4X4?
If we took the same approach to building a car as we did to our organisational controls and capabilities what would be the result? Jason Ha takes a look under the bonnet.
Waiting for Godot and a Data Breach
Indy Dhami joins Estragon and Vladimir and looks at what Waiting for Godot can teach us about the attitudes companies should adopt towards security threats
Lessons From the Pit Lane
Anne Wood takes inspiration from Formula 1, and discusses how understanding our environments is crucial to having the winning infosec strategy.
Digital Vampires
Dixie Newman lifts the coffin lid on the vampire, and how they can hunt and feed upon us in the digital world too.
The importance of the captain’s log…
How can we ensure our IT management is smooth sailing? Emmanuel Nicaise sails the infosec sea and considers how to steer clear of stormy weather.

Jurassic Park – Based on a True Story…
Yes, really!I was recently looking for a change of direction in my information security career and was invited to an interview at a local company. I was instructed to prepare a 10 minute presentation on ...

Lessons from the Big Four – Shakespeare’s Tragic Heroes
I don’t know if the phrase “the bigger they come, the harder they fall” was around when Shakespeare was alive but it applies to his tragic heroes across the board. If we look at his ...

God Save Me From My Friends. I Can Protect Myself From My Enemies
This quote is attributed to many. In fact, most people believe it was first said by King David himself. Some attribute to the French philosopher Voltaire, and others to the French marshal Claude Louis Hector ...
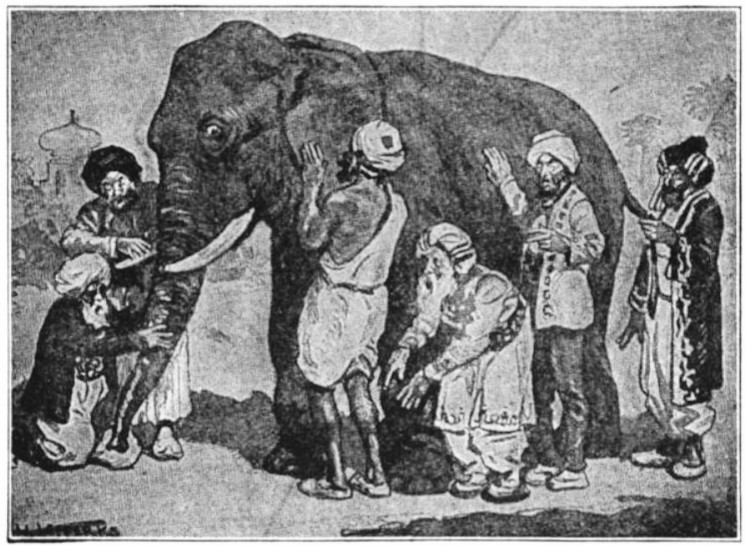
The Elephant and the Six Blind Men: What Does Information Security Mean to You?
The poem “The Blind Men and the Elephant” was written by John Godfrey Saxe (1816-1887). The essence of the poem is that their reactions were: The first felt the side of the elephant and said: It’s ...

Don’t Walk on the Grass!
In a vain bid to keep fit, I go running. Sometimes. When the mood takes me. It’s one of those things that I know I should do - I understand the importance of exercise, but ...

The Anxious Ant and the Lazy Grasshopper
Description: An 18th century coloured print by Jean-Baptiste Oudry from his luxury edition of Aesop's Fables Author: Jean Baptise This is an English translation of Jean Loup-Richet's original 'La Fourmi Soucieuse et la Cigale Paresseuse' analogy posted 28th ...
Spinning Jenny
James Hargreaves Spinning Jenny had a profound effect on the British textile industry, but its path from invention to mass market was not without incident.
The Elephant and the Six Blind Men: What Does Information Security Mean to You?
Eduardo Gelbstein examines John Godfrey Saxe’s poem “The Blind Men and the Elephant” and looks at how the lack of a holistic view of information security leads to confusion and weak governance.
Paralysis By Analysis
Can you spend too much time thinking before acting? Kristof Dewulf explores how trying too hard can often lead to failure.
Just the Tip of the Iceberg
It’s not what you can see above the water but below that matters with icebergs. Charles Sweeney looks at if the same is true of the web itself.
There’s No Such Thing as a Gruffalo… Until You Meet One
Mike Carter takes a look at storytelling for children and asserts that the imagination of employees is a powerful asset in the security culture of an organisation
Your Organization’s Central Nervous System: SIEM and Monitoring
Just as the human body needs a Central Nervous System, Alicia Smith explores whether a Security Information and Event Management system is the InfoSec equivalent